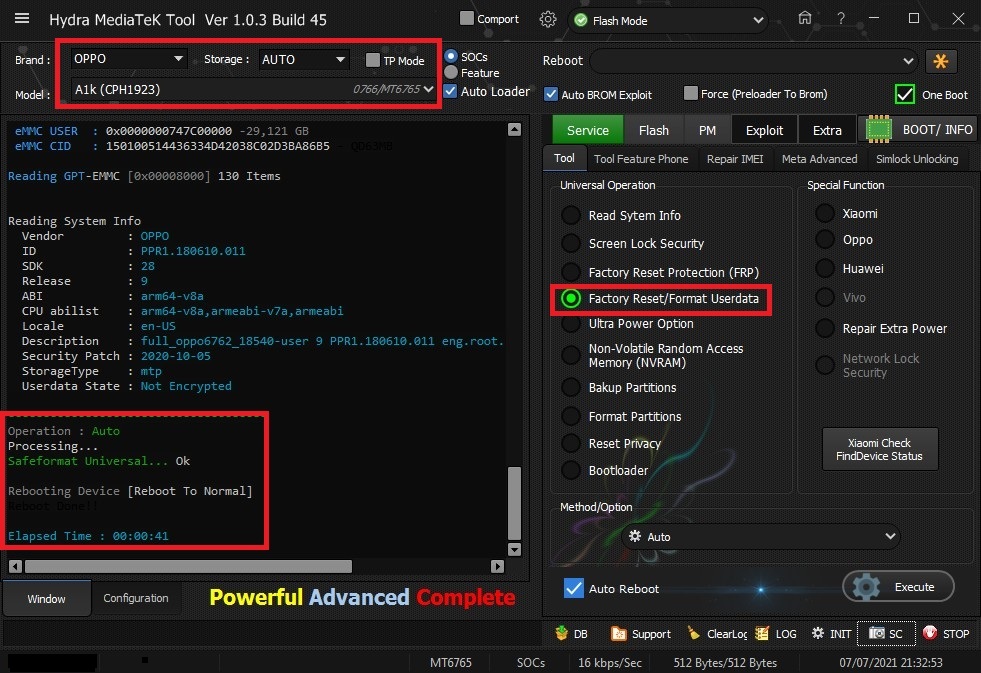
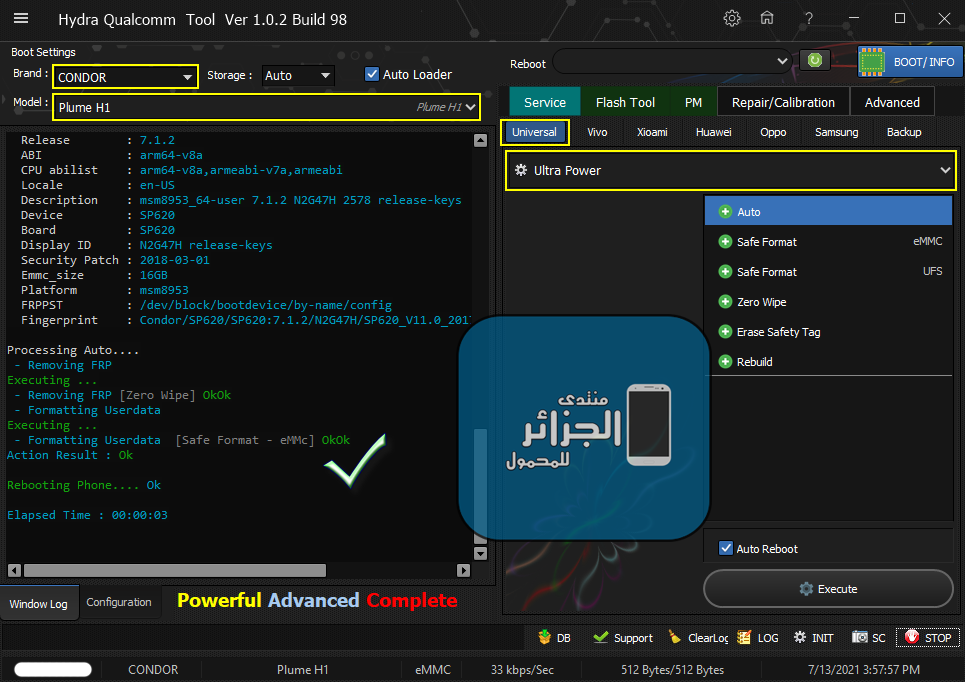
رد: تجارب الأعضاء الناجحة فى تصليح و تفليش و فك شفرات الأجهزة على Hydra Dongle
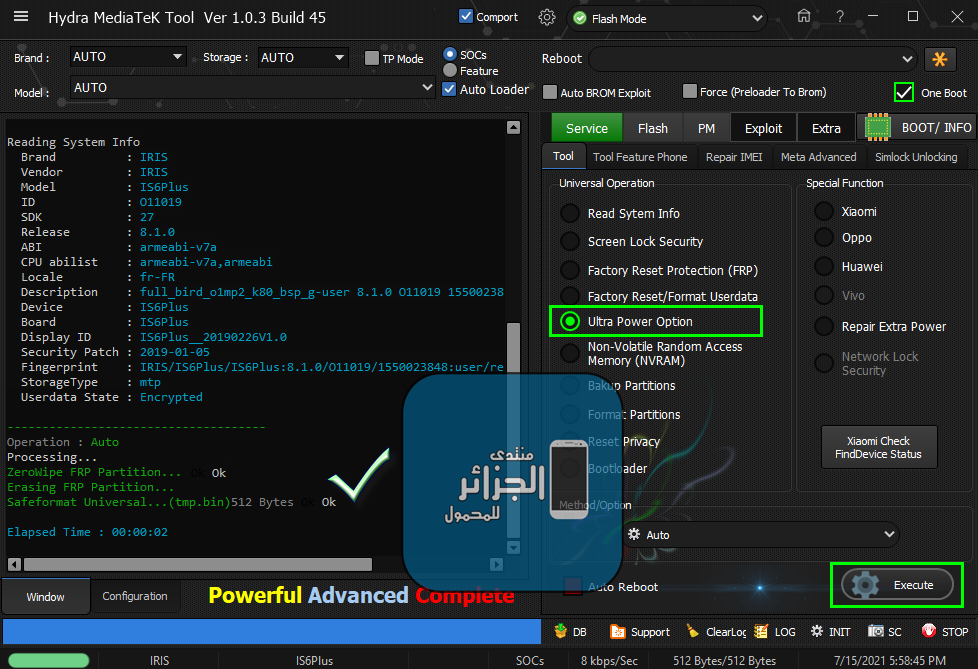
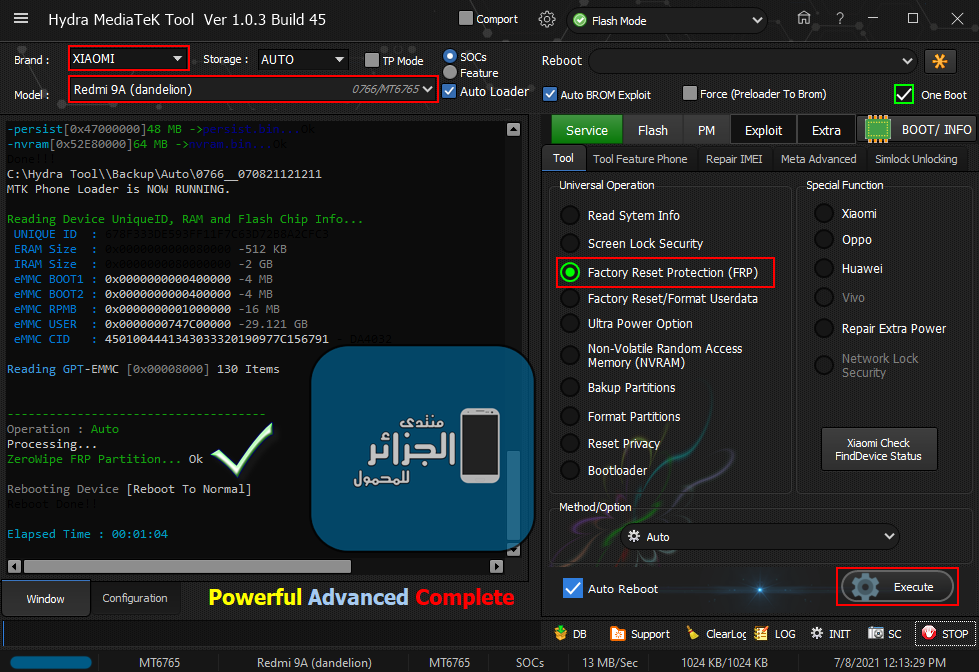
Xiaomi Redmi 9A (dandelion) Remove FRP Done
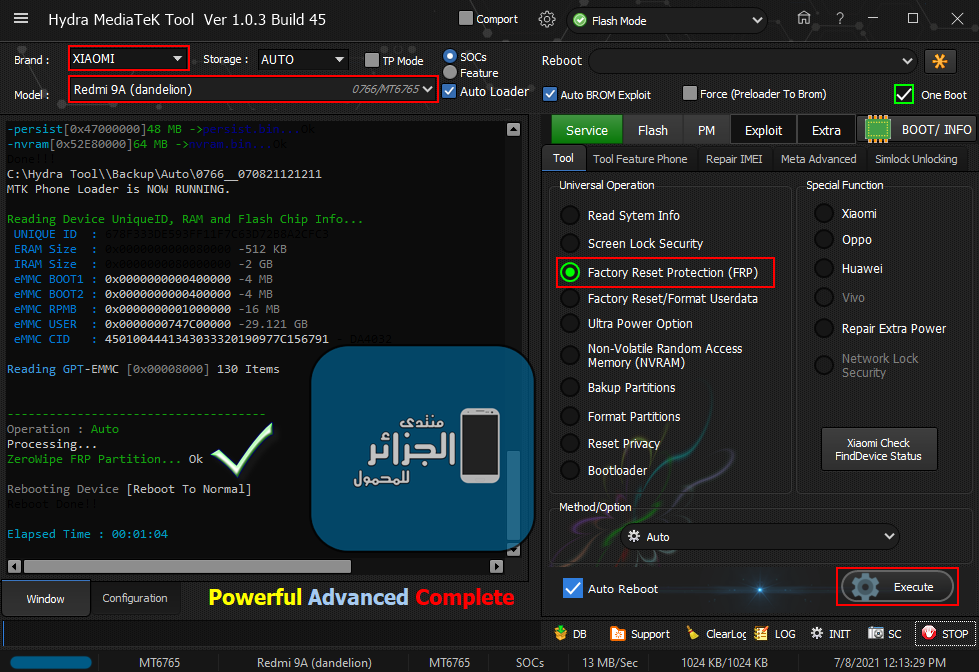
Xiaomi Redmi 9A (dandelion) Remove FRP Done
كود:
[B][FONT=Arial Black][SIZE=2]Searching for MTK Device...Found
Port Identification :Flashmode BROM
FriendlyName :MediaTek USB Port_V1632 (COM6)
Device :6&12e3c9ed&0&1
SymbolicName :\??\USB#VID_0E8D&PID_0003#6&12e3c9ed&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :01/22/2015,3.0.1504.0
Handshaking...Ok
Identifying Hardware ID.....
Reading Device hardware info..
hw code : 0766MT6765 [6765]
hw subcode : 8A00
hw version : CA00
sw version : 0000
Target config : E7
SB : 01 (True)
SLA : 02 (True)
DAA : 04 (True)
Exploiting Device...
Exploit Sent..
Successfully Exploited...
Handshaking...Ok
Identifying Hardware ID.....
Reading Device hardware info..
hw code : 0766MT6765 [6765]
hw subcode : 8A00
hw version : CA00
sw version : 0000
Target config : 00
SB : 00 (False)
SLA : 00 (False)
DAA : 00 (False)
FUSEID : 00000000
SECURE VERSION : 00
BL VERSION : FE
NORMAL BOOT
Preparing Download Agent..
DA : 6765_Xiaomi_wb.bin
Agent: MTK_DOWNLOAD_AGENT -HYDRA
Ver : MTK_AllInOne_DA_v3.3001.2020/03/17.ÉÏÎç10:04_497508
Init : Loader [1]
Sending : Accepted
Identifying Protocol...
Protocol : New
Synchronization...SYNC
Mode : brom
Preloader Initialization...
Parsing preloader_redmi9a_Hydra_V2.bin
Init : Accepted
Execute Secondary Loader
Init : Loader [2]
Executing : SYNC
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : 678F333DE593FF11F7C63D72B8A2CFC3
ERAM Size : 0x0000000000080000 -512 KB
IRAM Size : 0x0000000080000000 -2 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000001000000 -16 MB
eMMC USER : 0x0000000747C00000 -29.121 GB
eMMC CID : 4501004441343033320190977C156791 - DA4032
DA Speed : high-speed
Reading GPT-EMMC [0x00008000] 130 Items
Autobackup Partitions
-preloader[0x00000000]512 KB ->preloader.bin...Ok
-> Renaming Preloader.... preloader_k62v1_64_bsp.bin
Creating Scatter file... C:\Hydra Tool\\Backup\Auto\0766__070821121211\MT6765_Android_scatter.txt
-pgpt[0x00000000]32 KB ->pgpt.bin...Ok
-frp[0x3BD88000]1024 KB ->frp.bin...Ok
-nvdata[0x3DE88000]64 MB ->nvdata.bin...Ok
-protect1[0x45522000]8 MB ->protect1.bin...Ok
-protect2[0x45D22000]10.867 MB ->protect2.bin...Ok
-persist[0x47000000]48 MB ->persist.bin...Ok
-nvram[0x52E80000]64 MB ->nvram.bin...Ok
Done!!!
C:\Hydra Tool\\Backup\Auto\0766__070821121211
MTK Phone Loader is NOW RUNNING.
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : 678F333DE593FF11F7C63D72B8A2CFC3
ERAM Size : 0x0000000000080000 -512 KB
IRAM Size : 0x0000000080000000 -2 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000001000000 -16 MB
eMMC USER : 0x0000000747C00000 -29.121 GB
eMMC CID : 4501004441343033320190977C156791 - DA4032
Reading GPT-EMMC [0x00008000] 130 Items
-------------------------------------
Operation : Auto
Processing...
ZeroWipe FRP Partition... Ok
Rebooting Device [Reboot To Normal]
Reboot Done!!
Elapsed Time : 00:01:04
[/SIZE][/FONT][/B]