السلام عليكم
قراءة النمط
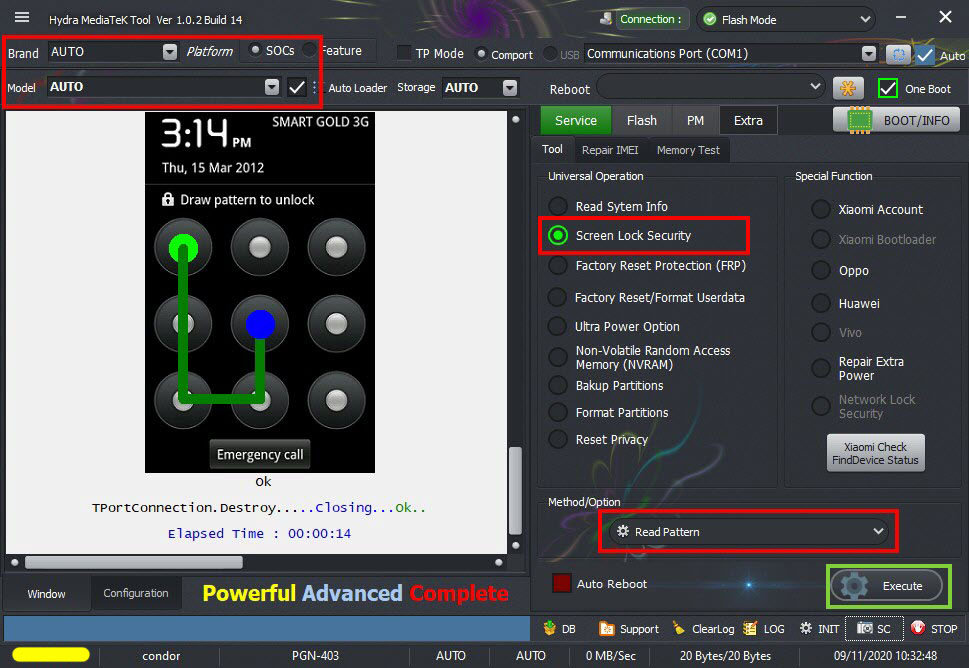
Condor C4+ (PGN-403) Read Pattern
by Hydra Dongle
قراءة النمط
Condor C4+ (PGN-403) Read Pattern
by Hydra Dongle
كود:
[B]******* Dongle Info *******
Version : Hydra Tool v 1.2
Serial : *******
Initialize : OKAY
Status : Activated
Life : 0 [0-0-0-0-0]
Brand : AUTO Model : AUTO Connection : Flash Mode
=====================================
Connection[WAITING]Found[PreLoader][COM10]
TPortConnection.Create...(COM10)..Opening...Ok
Handshaking...Ok
Identifying Hardware ID.....
BROM CPUID : 6572 (0000)MT6572[6572]
BROM HW_SW_VER : 8A00 CA01 0000 0000
FUSEID : 804001E0
SECURE VERSION : 00
BL VERSION : 00
BR Secured : 00
NORMAL BOOT
Preparing Download Agent..
DA : 6572.bin
Agent: MTK_DOWNLOAD_AGENT -HYDRA
Ver : MTK_AllInOne_DA_v3.3001.2018-09-18.13:22_452898
Init : Loader [1]
Sending : Accepted
Identifying Protocol...
Protocol : Old - eMMC
0000000000000000000000000000
PRMMCCID : 1501004E35585A4D4201A17ECEF1222D
Init Configuration
Running DA 4.2 on BBID : 0x88 Ok
Initializing Loader [2]
Sending Loader [2] Accepted
Reading Flashchip data....
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000000080000 -512 KB
eMMC USER : 0x00000000E9000000 -3,641 GB
ERAM Size : 0x0000000020000000 -512 MB
IRAM Size : 0x0000000000020000 -128 KB
UNICAL RID : E5C4B484078304615C58267740D0EA14
eMMC CID : 4E0001154D5A58357EA101422D22F1CE
Change to HIGH SPEED...
5A
Connection[WAITING]Found[COM16]
Reading Partition Table
SIZE[0x00000840] 22 Items > Done
Reading System Info
Brand : condor
Vendor : SPA_CONDOR_ELECTRONICS
Model : PGN-403
ID : JDQ39
SDK : 17
Release : 4.2.2
ABI : armeabi-v7a
Description : gionee72_wet_jb3-user 4.2.2 JDQ39 eng.android.1433299476 test-keys
Device : condor
Board : PGN-403_wet_jb3
Display ID : PGN-403
Fingerprint : alps/gionee72_wet_jb3/gionee72_wet_jb3:4.2.2/JDQ39/1413176904:user/test-keys
StorageType : mtp,mass_storage
Userdata State : Not Encrypted
Autobackup Partitions
-PRELOADER[0x00000000] 512 KB -> PRELOADER.bin...Ok
-> Renaming Preloader.... preloader_gionee72_wet_jb3.bin
Creating Scatter file... C:\Hydra Tool\\Backup\Auto\condor_PGN-403_6572--4.2.2_PGN-403_091120103228\MT6572_Android_scatter.txt
-NVRAM[0x01000000] 5 MB -> NVRAM.bin...Ok
Done!!!
C:\Hydra Tool\\Backup\Auto\condor_PGN-403_6572--4.2.2_PGN-403_091120103228
MTK Phone Loader is NOW RUNNING.
Reading System Info
Brand : condor
Vendor : SPA_CONDOR_ELECTRONICS
Model : PGN-403
ID : JDQ39
SDK : 17
Release : 4.2.2
ABI : armeabi-v7a
Description : gionee72_wet_jb3-user 4.2.2 JDQ39 eng.android.1433299476 test-keys
Device : condor
Board : PGN-403_wet_jb3
Display ID : PGN-403
Fingerprint : alps/gionee72_wet_jb3/gionee72_wet_jb3:4.2.2/JDQ39/1413176904:user/test-keys
StorageType : mtp,mass_storage
Userdata State : Not Encrypted
-------------------------------------
Operation : Read Pattern
Processing...
Searching PatternKey : . Found
Gesture Data : 2741E90F9E782047D46151F91BD7955C240A8A5E
Bruteforcing pattern hash..Please wait for few seconds
[COLOR="#FF0000"]Pattern Code : 14785[/COLOR]
1 2 3
4 5 6
7 8 9
Ok
TPortConnection.Destroy.....Closing...Ok..
Elapsed Time : 00:00:14[/B]